12.1: Prelude to Sequences, Series and Binomial Theorem
- Page ID
- 5194
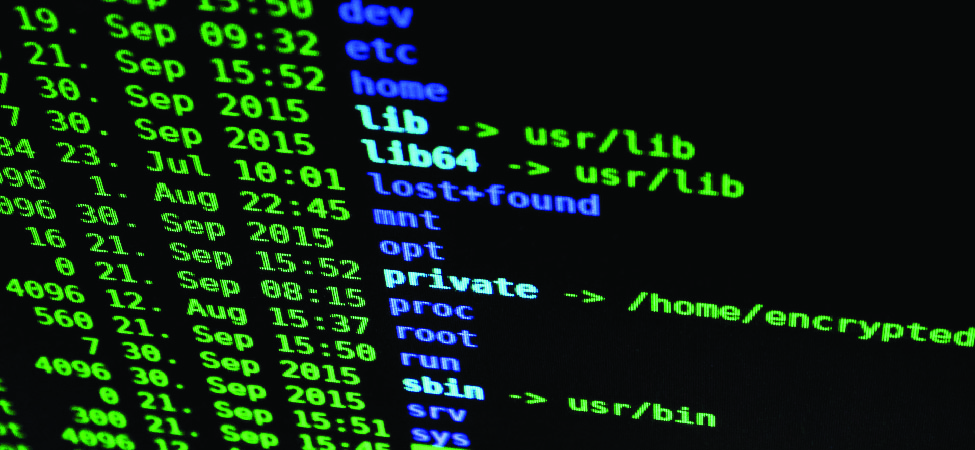
A strange charge suddenly appears on your credit card. But your card is in your wallet—it’s not even lost or stolen. Sadly, you may have been a victim of cyber crime. In this day and age, most transactions take advantage of the benefit of computers in some way. Cyber crime is any type of crime that uses a computer or computer network. Thankfully, many people are working to prevent cyber crime. Sometimes known as cryptographers, these people develop complex patterns in computer codes that block access to would-be thieves as well as write codes to intercept and decode information from them so that they may be identified. In this chapter, you will explore basic sequences and series related to those used by computer programmers to prevent cyber crime.